A Maltese research team has developed a system that transforms the unique contours of your face and palm into a cryptographic key without ever storing a single biometric record.
Every day, billions of people trust a handful of characters, like a password, a PIN, or a six-digit code, to guard their most sensitive digital lives. Despite decades of technological progress, the weakest link in digital security remains stubbornly human: we forget passwords, reuse them, share them, and lose them. The answer may lie in the human body itself.
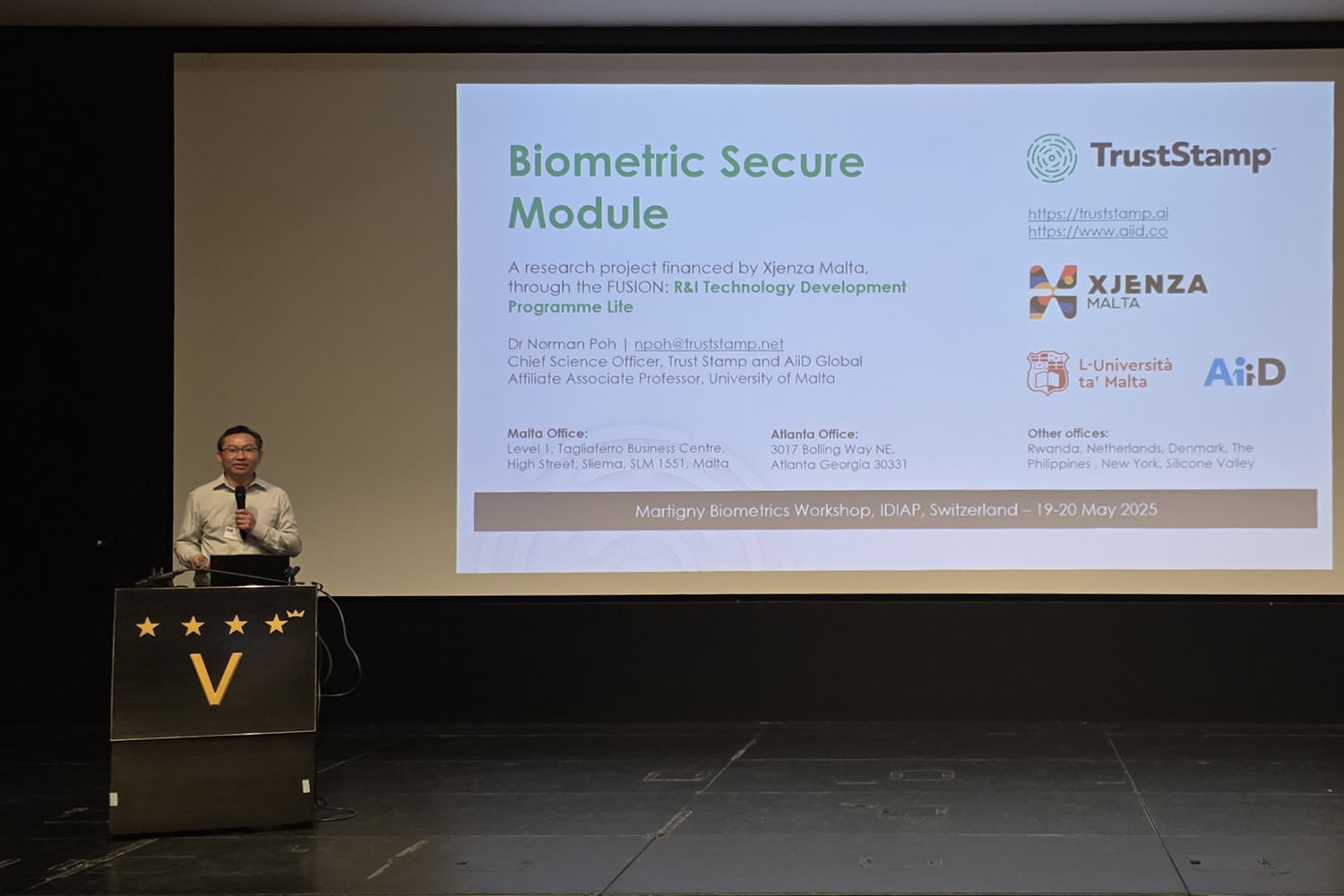
A team at Trust Stamp Malta has been working on exactly that problem. The project, called the Biometric Secure Module (BSM), is the result of an 18-month innovation initiative financed through Xjenza Malta’s FUSION: R&I Technology Development Programme Lite. The research and development phase is now close to the finishing line.
Biometrics Meets Cryptography
Biometrics is the use of physical characteristics, such as fingerprints, faces, or the geometry of our palms, to uniquely identify a person. Cryptography, meanwhile, secures information through mathematical transformation, relying on ‘keys’ – long strings of data used to encrypt and decrypt information. A strong cryptographic key is essentially impossible to guess, but wherever it is stored, it can potentially be stolen.
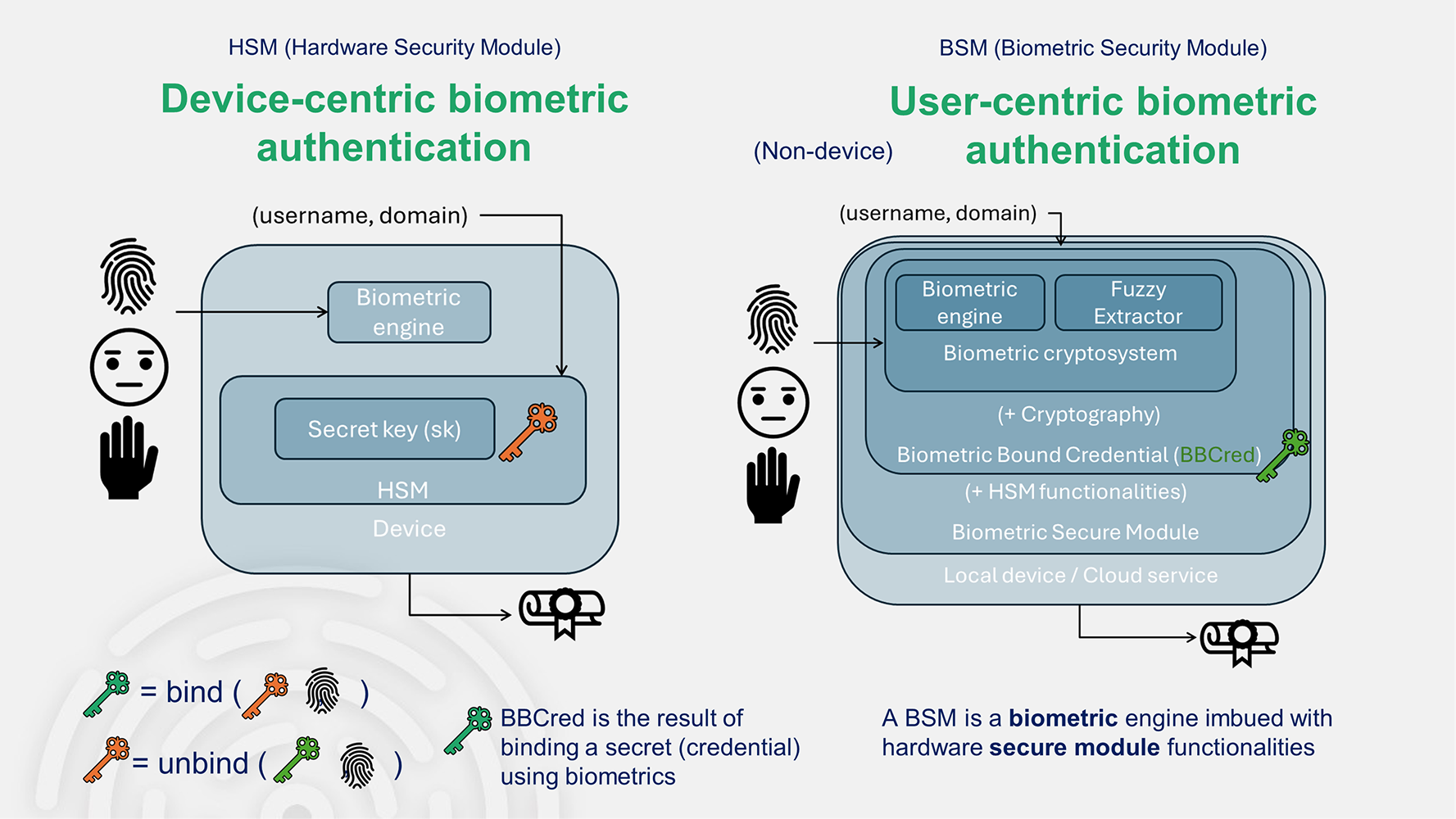
The BSM project bridges these two domains. Instead of generating a cryptographic key and storing it, the system generates the key directly from a person’s biometric features, on the spot, every time it is needed. The key is never stored anywhere. It exists ephemerally during authentication, and then it is gone.
Face and Palm: A Bimodal Approach
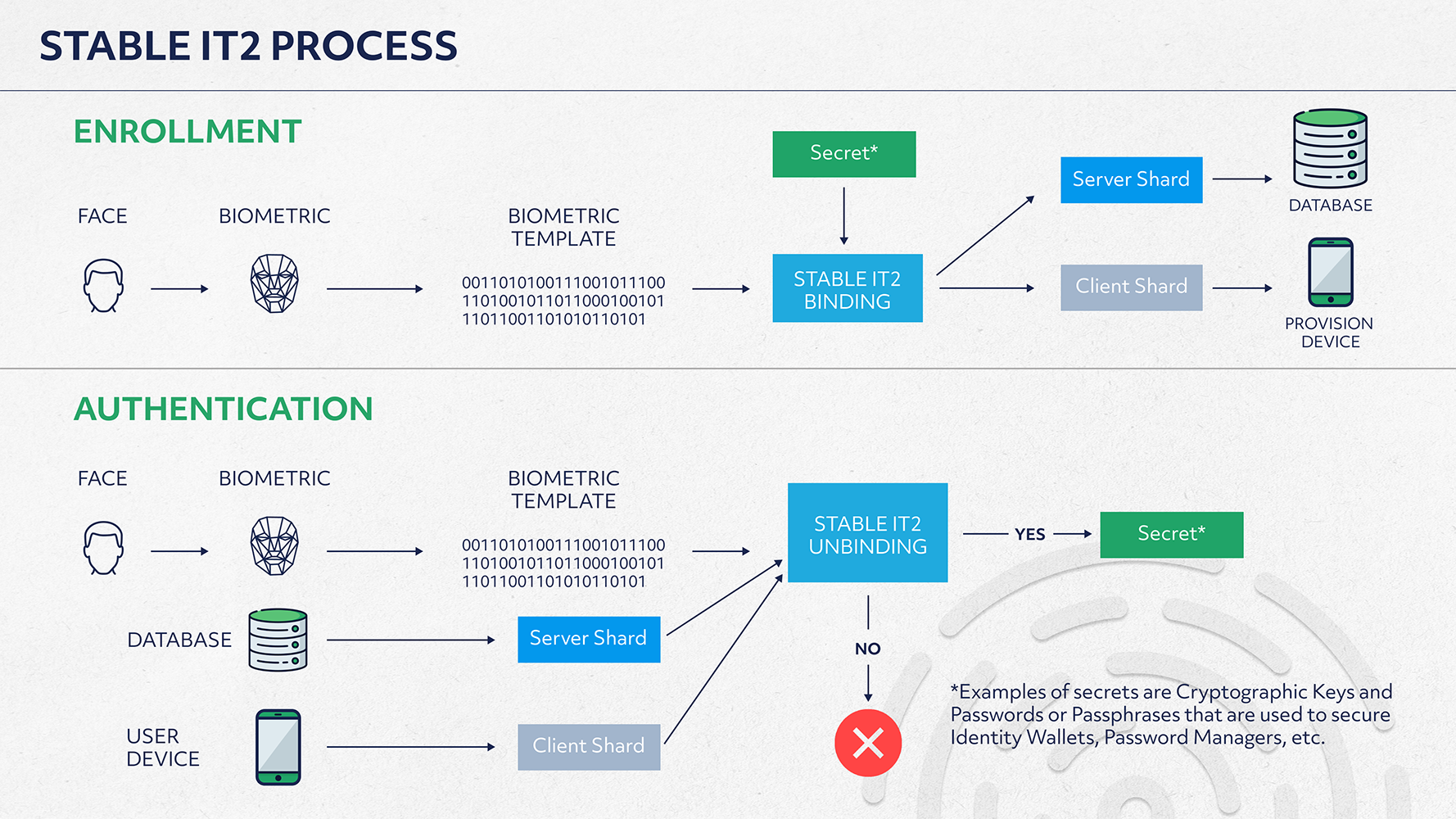
The engine behind BSM is Trust Stamp’s proprietary Stable IT2 algorithm. The system is ‘bimodal’ because it draws on two distinct inputs: facial recognition, which maps distances between features to produce a unique numerical representation of a face, and palm geometry, which analyses the shape and surface patterns of the hand without any physical contact.
Using both together produces a richer, more stable, and more private dataset from which a cryptographic key of sufficiently high complexity, what engineers call ‘high entropy’, can be derived. The system functions as a software-emulated hardware security module (HSM). An HSM is traditionally a dedicated physical device for managing cryptographic keys; here, it is delivered entirely in software for standard smartphones and mobile devices, with no specialist hardware required.
Privacy by Design
Most biometric systems store a record of your physical features in a database. If that database is breached, there is no remedy; you cannot change your face! The Stable IT2 algorithm sidesteps this entirely. Because the key is only regenerated from a fresh biometric input each time it is needed, the system stores neither raw biometric data nor the key itself. Even if the device were compromised, an attacker would gain nothing of value.
Palm geometry adds an extra layer of protection. Unlike facial images, which are captured constantly in public spaces and shared on social media, a person’s palm geometry remains, for most people, genuinely private.
From Research to Real-World Impact
The team has developed a software development kit (SDK) for integration into mobile applications, enabling the technology to be embedded into existing platforms without requiring new hardware. The most immediate use cases lie in financial services: banks, digital wallets, and payment platforms, where the combination of high security and regulatory compliance is a constant imperative. Identity access management providers and healthcare platforms, where the consequences of a security breach can extend far beyond financial loss, represent further target sectors.
The system aligns with authentication standards promoted by the FIDO Alliance, an industry body whose recommendations underpin passkey technology, the approach now adopted by the world’s largest technology platforms as a replacement for traditional passwords.
The Future of Identity
Biometrics are simultaneously becoming more powerful and more contested – celebrated for their convenience, but scrutinised for their risks. The BSM project offers a compelling answer: by ensuring that biometric data is processed but never retained, it demonstrates that strong authentication and meaningful privacy protection are not mutually exclusive goals. Our humanness can be the key without ever becoming a liability.
Malta’s Role in Global Cybersecurity
The BSM project would not have been possible without targeted public investment in research and innovation. The project was financed by Xjenza Malta, through the FUSION: R&I Technology Development Programme Lite. The funding covers 75% of the project costs, with Trust Stamp contributing the remaining from its own resources.
This model of co-investment, where public funding de-risks early-stage research while private expertise drives innovation, reflects a deliberate strategy to build Malta’s capacity as a knowledge economy. For a small island nation, the ability to attract and retain technology companies capable of conducting internationally relevant research is not incidental to economic development, but it is central to it. The BSM project joins a growing body of work in cybersecurity, fintech, and AI emerging from the Maltese research ecosystem.
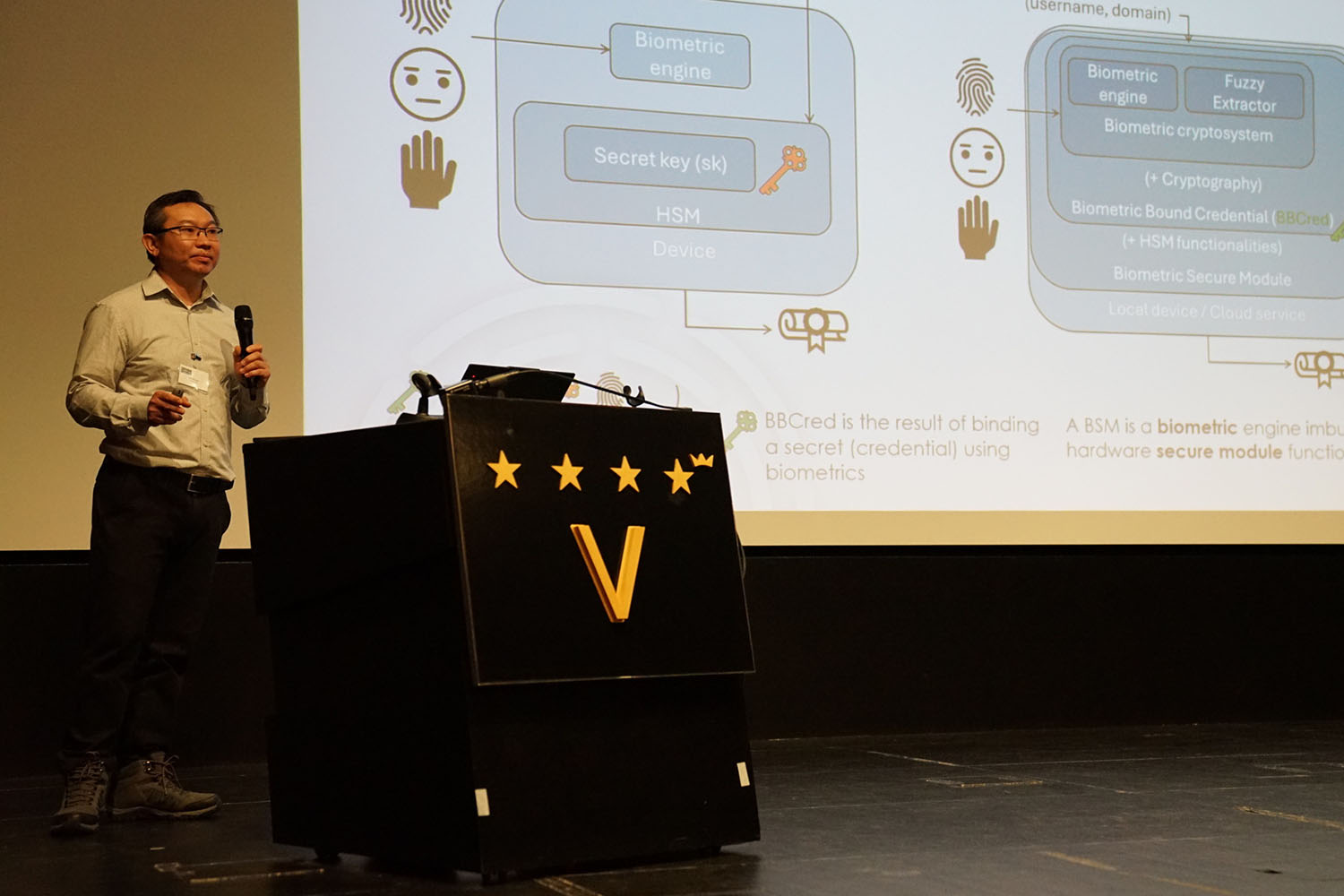
Dr Norman Poh and Dr Leanne Attard at the Martigny Biometrics Workshop in Switzerland (Photo courtesy of Trust Stamp Malta)

Further Reading
Trust Stamp. (2024). Trust Stamp’s Biometric Authentication with Stable IT2 – A Path from Passwords to FIDO, Passkeys and Beyond.
FIDO Alliance. (2024). FIDO attestation: Enhancing trust, privacy, and interoperability in passwordless authentication.
Norman Poh. (2025). Advancing Security with Biometric-Bound Credentials: A New Era in Digital Identity. Trust Stamp.


Comments are closed for this article!